+31 (0)43 30 88 400 | office@comex.eu
Partner resources
On this page, you will find several materials to support you in selling and positioning FAST LTA solutions. Use these resources actively in your sales processes, marketing activities, and client meetings.
Are you missing something or do you need support with a specific project? Please contact us.


Case studies, white papers, and brochures
The most frequently used resources in conversations with potential clients are our case studies and brochures. You can find these as PDF downloads in our knowledge center. There are also several white papers available there that may be relevant for certain end users.
Other material
Infographics
Disclaimer. These infographics are indicative and intended for illustration purposes only. No rights can be derived from the content. Configurations and advice are always assessed and confirmed by Comex on a project-specific basis.
Active WORM Archive
This infographic explains the difference between backup and archive and shows how hardware WORM and an active archive contribute to ransomware protection, cost reduction, and compliance. Includes a comparison between Silent Bricks and Silent Cubes.
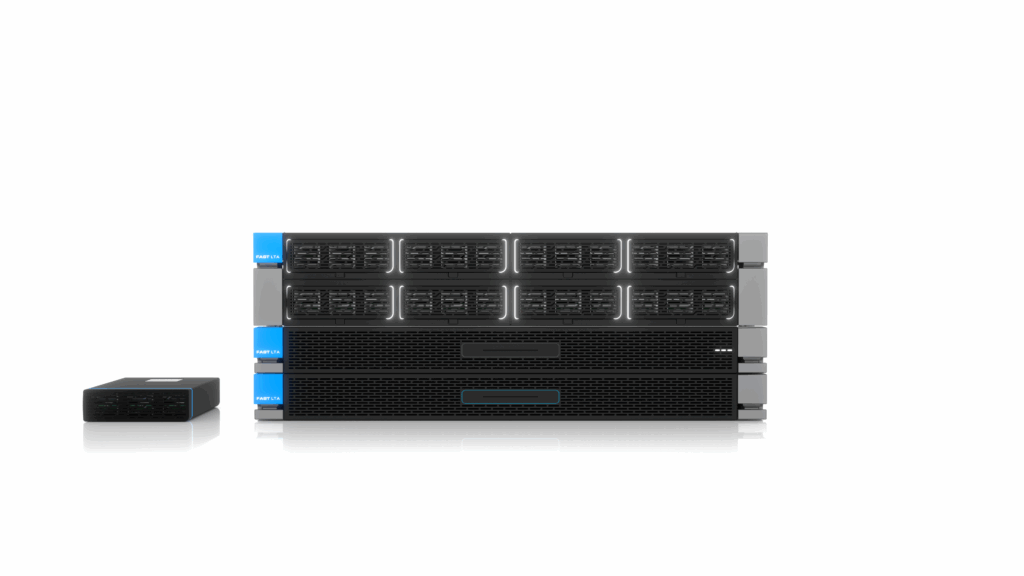
Silent AI
Overview of the Silent AI infrastructure with a focus on local AI power, scalable configurations, and fixed price tiers. This infographic shows how organizations can deploy AI without dependency on external cloud environments.
Zero Loss & AI
This infographic combines the 3-2-1-1-0 principle with hardware WORM and on-premises AI. It shows how Zero Loss storage and local AI work together to ensure maximum protection, data control, and long-term continuity.
Strategic (implementation) concepts
Disclaimer. The implementation concepts on this page serve as a general guideline and example architecture. No rights can be derived from the content.
Every environment, workload, and compliance requirement is unique. Final architecture choices, configurations, and advice are always assessed and validated by Comex on a project-specific basis.
Backup implementation concept
This document describes an example architecture for a modern 3-2-1-1-0 backup strategy with Silent Bricks. It covers performance versus capacity tiers, geo-replication, physical air-gap, S3 Object Locking, and advanced integrity mechanisms such as Erasure Coding and Digital Audit. Aimed at IT architects who want to achieve maximum recovery certainty and Zero Loss.
Zero Loss implementation concept
This document describes an example architecture for the transition to a Zero Loss environment for secondary storage. It covers the combination of Silent Bricks and Silent Cubes, hardware-based WORM sealing, physical air gap, compliance requirements such as NIS2 and DORA, and the migration from tape to modern disk-based storage. Aimed at organizations that want to achieve maximum ransomware resilience and audit-proof archiving.
Other documentation
Disclaimer. The documents in this section contain conceptual designs and technical approaches intended for inspiration and as a general guide. They provide insight into possible architectures, configurations, and application scenarios regarding FAST LTA solutions. Since every environment and use case is unique, no rights can be derived from these documents.
WORM and audit-proof archiving
This document provides a conceptual overview of WORM storage and the role of audit-proof archiving within a modern Zero Loss architecture. It covers the difference between backup and archive, hardware-based WORM, physical air gaps, and the role of active archives in ransomware protection and compliance. Aimed at organizations that want to ensure long-term data integrity and control over their archive data.
Strategic necessity of local infrastructure and on-prem AI
This document discusses the strategic role of local infrastructure and on-premises AI in the context of digital sovereignty. It addresses the risks of cloud dependency, the rise of Shadow AI, and the need for local AI platforms such as Silent AI. Additionally, it demonstrates how Zero Loss storage with Silent Bricks and Silent Cubes forms the foundation for secure, controllable, and compliance-proof data infrastructures.
Navigating the AI revolution
This document provides a practical overview of the risks and challenges surrounding Shadow AI and the use of public AI tools within organizations. It covers key themes such as data leaks, compliance, governance, and the financial impact of uncontrolled AI usage. Furthermore, it introduces local AI solutions like Silent AI as a secure alternative for organizations looking to combine innovation with control over their data.
Strategic compliance guide with FAST LTA systems
This document describes how organizations can align their data infrastructure with European regulations such as NIS2, DORA, and GDPR. It covers the role of hardware WORM, audit-proof archiving, and physical air gaps in achieving a Zero Loss strategy. Additionally, it shows how Silent Cubes and Silent Bricks contribute to compliance, ransomware protection, and long-term data integrity.
Zero Loss strategy for cyber resilience
This document describes a technical security concept for modern backup and archiving environments. It addresses the shift in the threat landscape, the limitations of traditional backup strategies, and the role of hardware WORM, immutability, and physical air gaps in a Zero Loss architecture. It also explores the use of Silent Bricks, Silent Cubes, and local AI as a foundation for cyber resilience, compliance, and digital sovereignty.

 Subscribe for tips and info
Subscribe for tips and info